Cloud computing and identity security are two of the most important pillars of modern IT infrastructure. As organizations continue to migrate systems, applications, and data into the cloud, the need for professionals who understand both cloud architecture and cybersecurity principles has grown rapidly. Platforms like Microsoft Azure are now widely used across industries to support scalable infrastructure, remote work environments, and secure access to enterprise resources.
As part of my ongoing development in cybersecurity and cloud technologies, I recently completed several Microsoft Learn modules covering Azure compute services, networking fundamentals, and identity management through Microsoft Entra ID. These modules included hands-on labs where I deployed my first Azure Virtual Machine and explored how identity and access management systems help secure modern cloud environments.
This blog post highlights some of the key concepts I learned during this training. I will discuss the fundamentals of Azure infrastructure, including virtual machines, compute services, and networking architecture. I will also explore how identity management, authentication protocols, and the Zero Trust security model play a critical role in protecting cloud environments.
Understanding how cloud infrastructure and identity security work together is essential for anyone pursuing a career in IT, cloud engineering, or cybersecurity. By learning these foundational technologies, professionals can better design, secure, and manage the systems that power modern organizations.
☁️ What Is Microsoft Azure Fundamentals (AZ-900)?
The AZ-900 Microsoft Azure Fundamentals learning path introduces core cloud concepts and Azure services used across modern organizations.
Key areas covered include:
- Azure Virtual Machines (VMs)
- Azure Virtual Desktop
- Containers and serverless computing
- Application hosting options
- Azure Virtual Networks
- VPN and ExpressRoute connectivity
- Azure DNS services
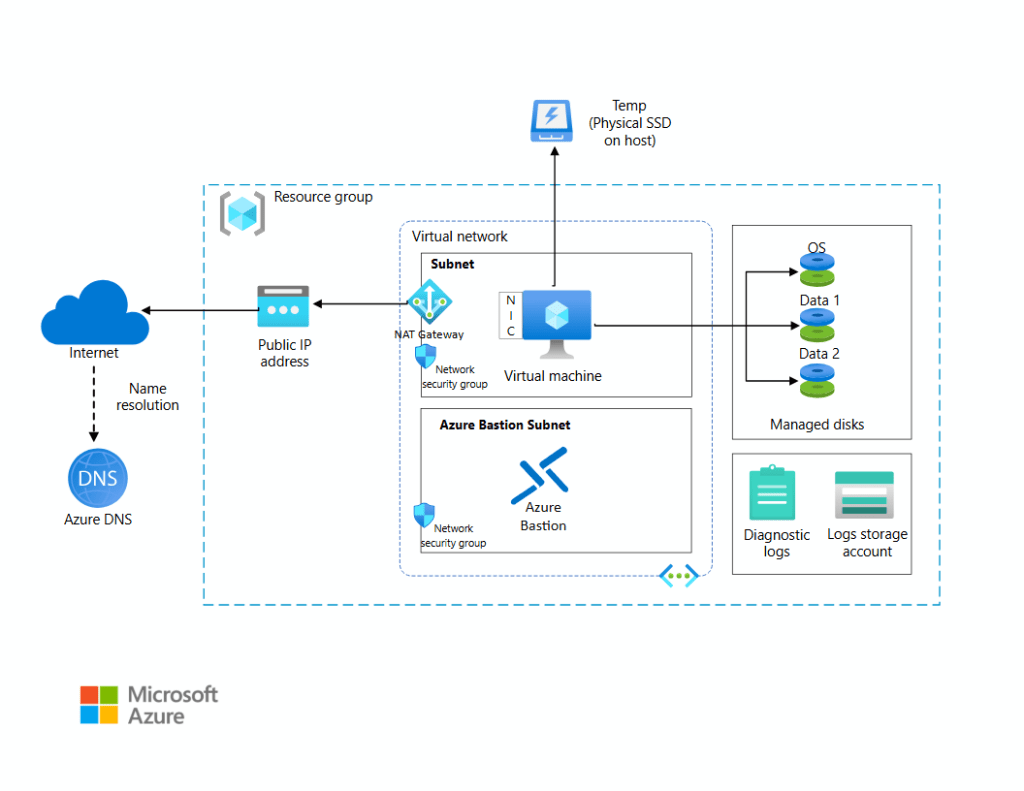
🖥️ Creating an Azure Virtual Machine
The most valuable parts of the training are completing labs in my opinion.
Deployment Steps:
- Creating a resource group
- Selecting an operating system image
- Configuring networking settings
- Assigning a public IP address
- Setting authentication credentials
- Reviewing security and monitoring options
This process demonstrates how Azure simplifies infrastructure deployment while maintaining enterprise level control.
Why This Matters in Real IT Roles
In traditional environments, making a server could take days or weeks. In Azure, infrastructure can be deployed in minutes.
⚙️ Azure Compute Services Explained
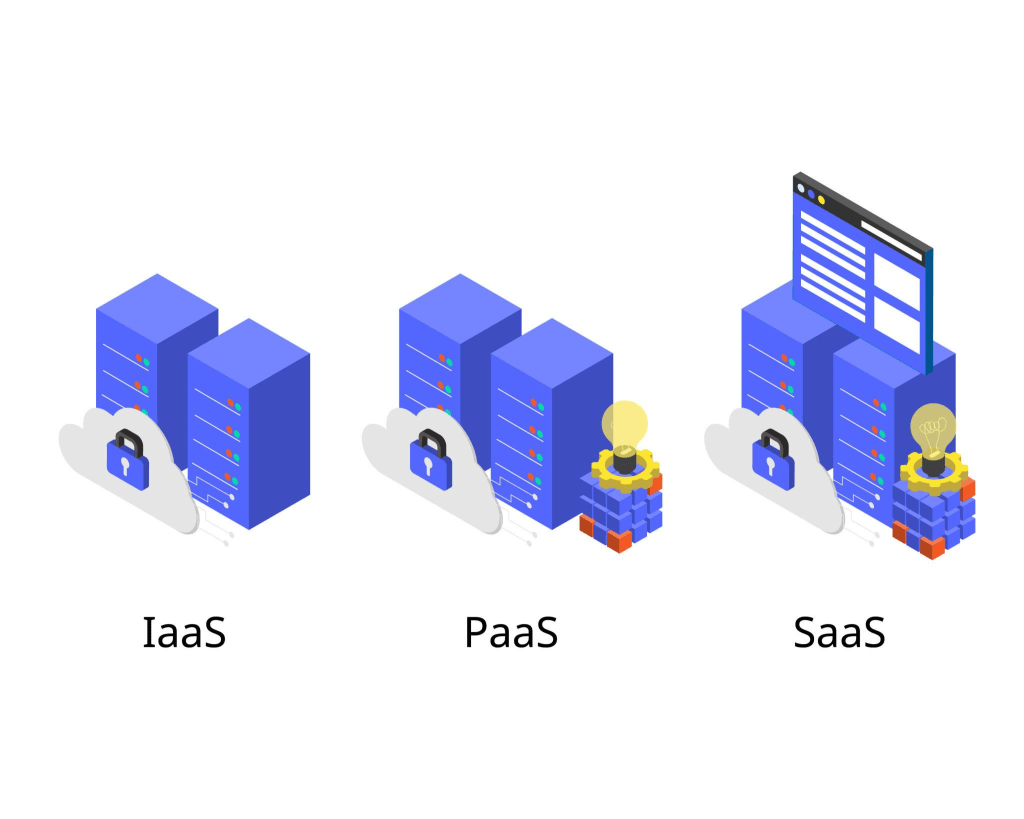
Microsoft Azure offers multiple compute models depending on workload.
Virtual Machines (Infrastructure as a Service)
Best for:
- Legacy applications
- Custom server configurations
- Migration from on prem environments
VMs provide full administrative control, similar to managing physical servers.
Containers
Best for:
- DevOps workflows
- Microservices architecture
- Consistent deployments across environments
Containers package applications with dependencies, reducing compatibility issues. I look forward to understanding and working with containers more.
Azure Functions (Serverless Computing)
Best for:
- Event driven automation
- Background processing
- Lightweight APIs
Serverless computing removes infrastructure management, allowing developers to focus only on code.
💻 Azure Virtual Desktop and Modern Work Environments
Azure Virtual Desktop enables organizations to host secure Windows environments in the cloud.
Common real world use cases include:
- Remote workforce solutions
- Secure contractor access
- Centralized desktop management
- Reduced endpoint security risks
This model has become very important as hybrid work environments continue to expand.
🌐 Understanding Azure Networking Fundamentals
Cloud infrastructure relies heavily on networking design. The training introduced several foundational services.
Azure Virtual Networks (VNets)
VNets function like a private network inside Azure, allowing secure communication between resources.
Benefits include:
- Network isolation
- Segmentation of workloads
- Secure internal communication
VPN Gateway vs ExpressRoute
Organizations connect on prem infrastructure to Azure using:
- VPN Gateway — encrypted connection over the public internet
- ExpressRoute — private dedicated connection to Microsoft datacenters
ExpressRoute is commonly used by enterprises requiring higher reliability and lower latency.
Azure DNS
Azure DNS manages domain name resolution while integrating seamlessly with cloud hosted applications and services.
🔐 Cloud Security Lessons from the Training
One important realization from this learning experience is that cloud security starts with architecture decisions.
Proper configuration of networking and access controls directly impacts security posture.
Core principles reinforced include:
- Least privilege access
- Public vs private endpoints
- Network segmentation
- Secure connectivity design
These concepts align closely with modern cybersecurity frameworks.
📈 Real World Applications for IT Professionals
Understanding Azure compute and networking services helps professionals:
- Transition from traditional IT infrastructure to cloud environments
- Support hybrid cloud deployments
- Improve scalability and reliability
- Strengthen cloud security knowledge
- Prepare for Azure certifications and cloud based roles
Even entry level cloud knowledge improves technical versatility in today’s job market.
🧠 Continuous Learning in Cloud Technology
One of the strengths of Microsoft Learn is its structured learning approach. Each module builds progressively, reinforcing concepts through hands-on experience.
This training expanded my understanding of:
- Infrastructure as a Service (IaaS)
- Application hosting strategies
- Cloud networking architecture
- Azure deployment workflows
Cloud technology evolves rapidly, making continuous learning essential for long term success in IT.
☁️Understanding Identity in the Cloud
At its core, identity management is about verifying who or what is accessing systems and determining what they are allowed to do.
Modern identity systems provide four primary capabilities:
- Authentication – proving that a user or system is who they claim to be
- Authorization – determining what resources that identity can access
- Administration – managing user identities and permissions
- Auditing – tracking activity for security and compliance purposes
These capabilities form the foundation of Identity and Access Management (IAM) systems used across cloud platforms.
According to the Microsoft Entra identity module, identity is considered the control plane for modern security, meaning it is the bread and butter used to determine access to applications, infrastructure, and data.
In a modern IT environment, identities can represent:
- Users
- Applications
- Devices
- Services
Each of these identities must be authenticated before granting access.
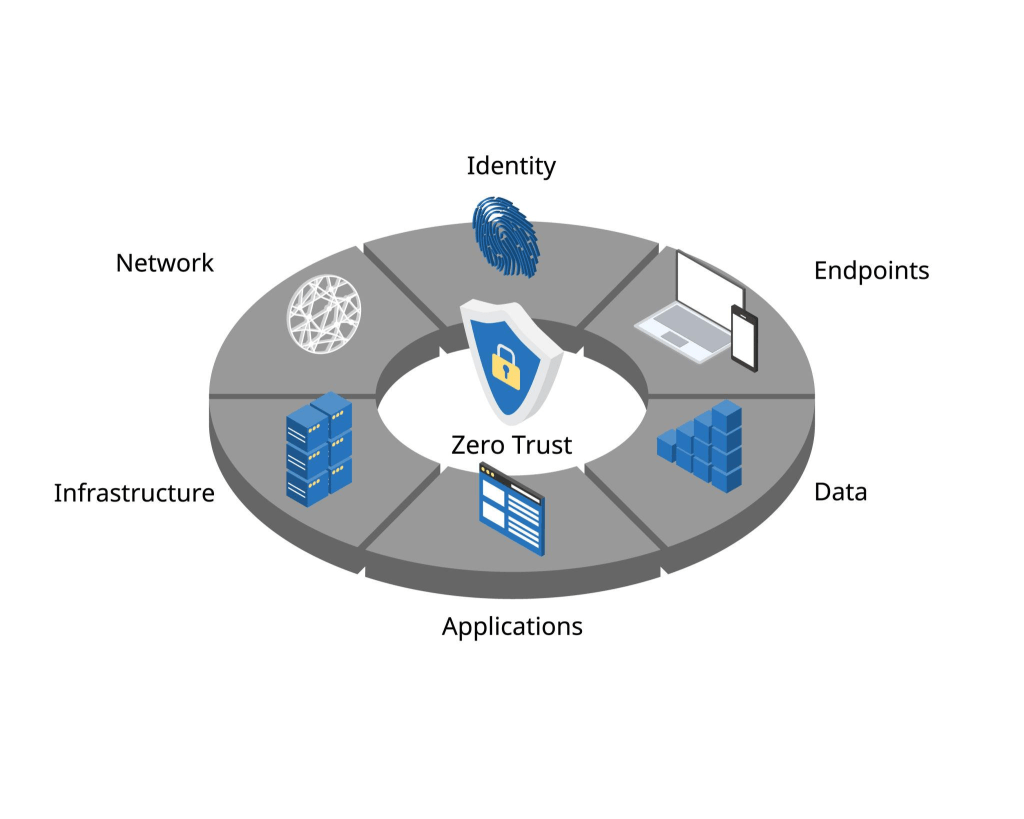
🔐Shift to Zero Trust Security
Traditional security models assumed that anything inside the network could be trusted. Unfortunately, modern cyber threats make that approach risky.
Organizations are moving toward a Zero Trust security model, which assumes that breaches are always possible.
The Zero Trust model is based on three principles:
1. Verify Explicitly
Every request for access must be validated using all available signals such as:
- user identity
- device health
- location
- risk indicators
2. Use Least Privilege Access
Users should only have the minimum permissions required to perform their job.
3. Assume Breach
Security architecture should be designed with the assumption that attackers may already have some access.
The diagram in the training module shows how this model expands security beyond the network perimeter to protect identities, devices, applications, data, infrastructure, and networks.
In practice, this means that access decisions are constantly evaluated rather than being granted permanently.
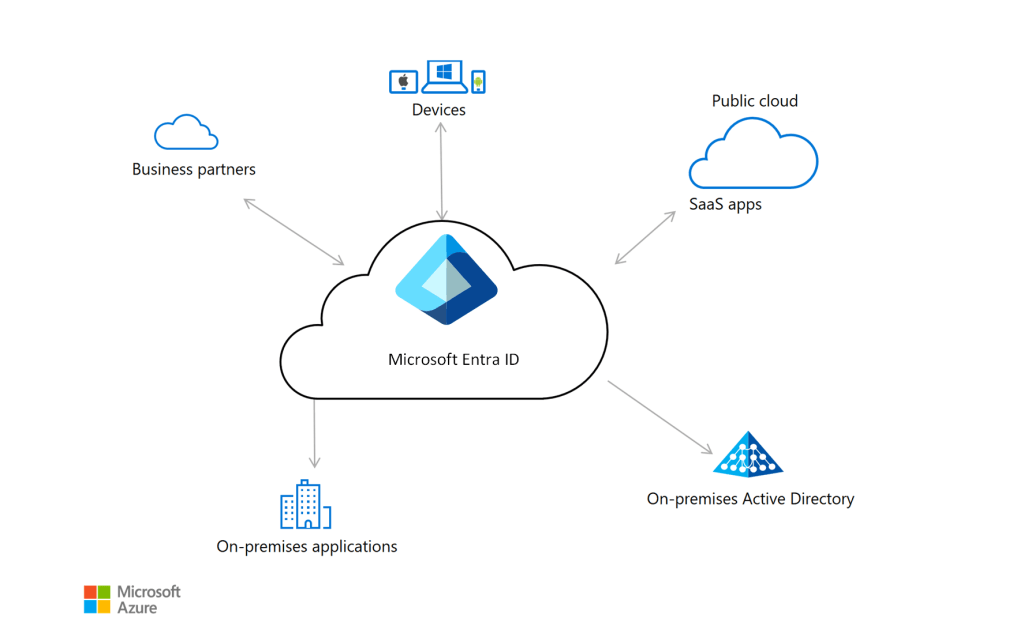
Microsoft Entra ID: Identity as a Service
Microsoft Entra ID is Microsoft’s cloud based identity and access management platform. It gives organizations with Identity as a Service (IDaaS) capabilities, allowing users to securely access applications and cloud services from anywhere.
Some core features include:
- Single Sign-On (SSO)
- Multi-Factor Authentication (MFA)
- Conditional Access policies
- Identity governance
- Integration with Microsoft 365 and Azure
Microsoft Entra ID allows organizations to manage identities centrally across both cloud and on-premises environments, which simplifies administration and improves security visibility.
Authentication and Identity Protocols
Modern identity systems rely on standardized protocols to securely authenticate users and applications.
Some of the most common protocols include:
OpenID Connect (OIDC)
An authentication protocol built on OAuth 2.0 that allows applications to verify a user’s identity.
Security Assertion Markup Language (SAML)
An XML-based protocol used to exchange authentication and authorization data between identity providers and service providers.
OAuth 2.0
A framework used primarily for authorization, allowing applications to access resources on behalf of users.
These protocols help enable secure single sign-on experiences while reducing password fatigue for users.
🖥️ Security Tokens and Claims-Based Identity
Modern authentication systems often rely on security tokens rather than constantly re authenticating users.
Three common types include:
- Access Tokens – used to access protected resources
- Refresh Tokens – used to obtain new access tokens
- ID Tokens – used to verify user identity
Many of these tokens are implemented using JSON Web Tokens (JWTs), which securely transmit identity information between systems.
JWTs contain claims, which are pieces of information about the user, such as their name, email address, or role within an organization.
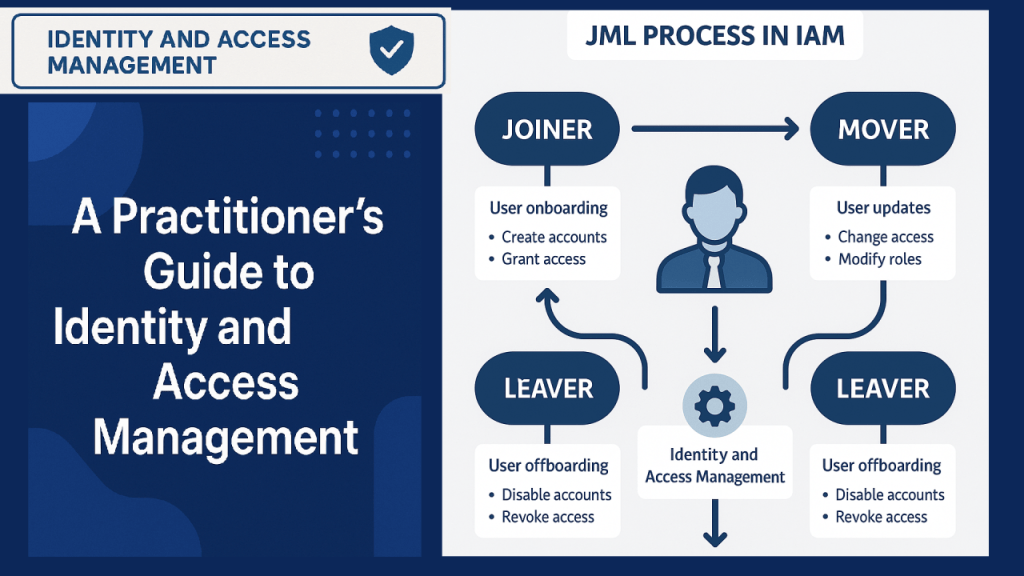
Identity Lifecycle Management
Another important concept I learned is identity lifecycle management, which focuses on managing digital identities throughout their entire lifecycle.
Most organizations follow a process known as:
Join – Move – Leave
- Join – creating identities for new employees or users
- Move – updating permissions when users change roles
- Leave – removing access when someone leaves the organization
Without proper lifecycle management, organizations can accidentally leave unused accounts active, which creates serious security risks.
Automating this process helps ensure that identities remain accurate and secure over time.
📈 Identity Governance and Auditing
Identity governance is the ongoing process of managing and monitoring identity systems to ensure security and compliance.
This includes:
- monitoring sign in logs
- reviewing access permissions
- tracking user activity
- detecting suspicious behavior
Microsoft tools such as Azure Monitor, Microsoft Sentinel, and Entra activity logs can provide visibility into authentication events and potential threats.
Effective governance ensures that only authorized users maintain access to critical systems.
🌐 Why Identity Security Matters in Cybersecurity
One of the biggest takeaways from studying identity security is that identity is now the front line of cybersecurity defense.
Attackers frequently target credentials through methods like:
- phishing
- credential stuffing
- password spraying
- session hijacking
Strong identity systems reduce these risks by enforcing:
- multi-factor authentication
- conditional access policies
- least privilege permissions
- continuous monitoring
When implemented properly, identity security significantly reduces the attack surface of an organization.
🎯 Final Thoughts: Why Azure Fundamentals and Identity Security Matter
Studying Azure infrastructure and identity management through Microsoft Entra ID helped me better understand how modern cybersecurity strategies protect organizations operating in cloud environments.
Deploying my first Azure Virtual Machine may seem like a beginner exercise, but it represents an important step toward understanding how cloud infrastructure is built, secured, and managed. Seeing how compute, networking, and identity systems work together reinforces how critical cloud knowledge has become for IT and cybersecurity professionals.
This training strengthened my understanding of:
✅ Core cloud computing concepts
✅ Azure compute and networking fundamentals
✅ Real-world infrastructure deployment
✅ Identity and access management principles
✅ Foundational cloud security practices
One of the biggest takeaways from this learning experience is how strongly modern security relies on identity first architecture and Zero Trust principles. Protecting identities, enforcing least privilege access, and continuously monitoring authentication activity are now essential parts of defending cloud environments.
As organizations continue adopting hybrid and cloud first infrastructure, cybersecurity professionals must understand how identity, networking, and compute services work together to protect digital systems.
As I continue my cybersecurity education, I plan to deepen my knowledge in areas such as:
- identity governance and lifecycle management
- cloud security architecture
- authentication and authorization protocols
- Microsoft security tools and monitoring platforms
Cloud computing is constantly evolving, which makes continuous learning essential. Completing this Azure training was an important milestone in my journey toward building stronger skills in cloud infrastructure, identity security, and cybersecurity operations.
Leave a comment